What is a VPN
What is a VPN anyway?
Put simply, a Virtual Private Network, or VPN, is a group of computers networked together over a public network—namely, the Internet. Businesses use VPNs to connect remote datacenters, and individuals can use VPNs to get access to network resources when they're not physically on the same LAN (local area network). VPNs are also particularly useful as a method for securing and encrypting internet communications when using an untrusted public network.
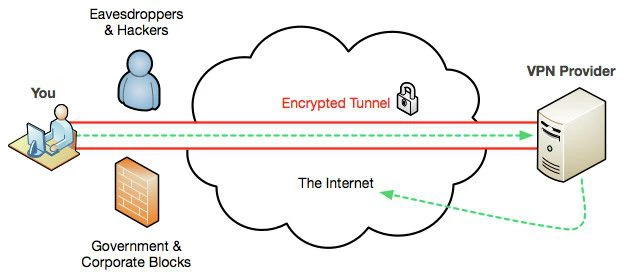
When you connect to a VPN, you usually launch a VPN client on your computer (or click a link on a special website) and log in with your credentials. Your computer then exchanges unique identifiers with a far away server to begin the encrypted connection. Once both computers have verified each other as authentic, all of your internet communication is encrypted and secured from eavesdropping.
Why would I use a VPN?
VPN users usually fall into a few separate categories:
- The student/worker. This person will use a VPN provided by their school or company to access resources on their network when they're at home or travelling.
- The privacy minded and security advocate. Whether they're in a strictly monitored environment or a completely free and open one, this person uses VPN services to keep their communications secure and encrypted at home or abroad. To them, unsecured connections mean someone's reading what you say.
- The international content viewer. This person uses a VPN to check out their favourite TV shows as they're interested in location-restricted content (which can also include internet radio), or to use a new web service or application that looks great but is limited to a specific country or region. For instance, before Netflix came to Australia, many people used VPNs to circumvent the US only restriction to watch Netflix shows.
- A combination of the above. In all of these cases, a VPN service can be helpful, whether it's just a matter of protecting yourself when you're out and about or whether you handle sensitive data for your job.
Australian Government metadata laws
A description of what types of data are collected is summarised nicely by crikey.com.au below:
"The legislated form of the dataset is very vague and there are likely to be differences of interpretation between companies, but it consists of subscriber or account holder details, the source and destination of a communication, date, time and duration of communication, location and what services was used e.g. voice, SMS, social media, Skype, and the type of delivery services (ADSL, Wi-Fi, VoIP, cable, etc)
It will not include browsing history and appears not to include download volumes."
With the introduction of these new metadata laws, ways to circumvent data collection have come into the spotlight (use of a VPN being such a method).
A VPN will cause communications between the sender and the VPN server to be encrypted. The only metadata that will be collected will show that the recipient’s data came from a VPN server.
But, again, there are things to be wary of. As with email, using a VPN server that is based in one of the “Five Eyes” countries is probably not a good idea. Even if the server is overseas, the VPN provider may well retain logs of who connected and when, which might be seized by that country’s law enforcement agency and, ultimately, identify the sender. The location of the VPN server, and their policy on retention of access logs are important considerations when choosing a VPN.
References: